warning
Pyroscope is now part of Grafana Labs! As a result we have consolidated efforts around our Grafana plugins to make one recomended way of using Pyroscope. As a result this blogpost is now outdated. However, you can find updated docs on how to add profiling to Grafana with Pyroscope using the Grafana profiling documentation.
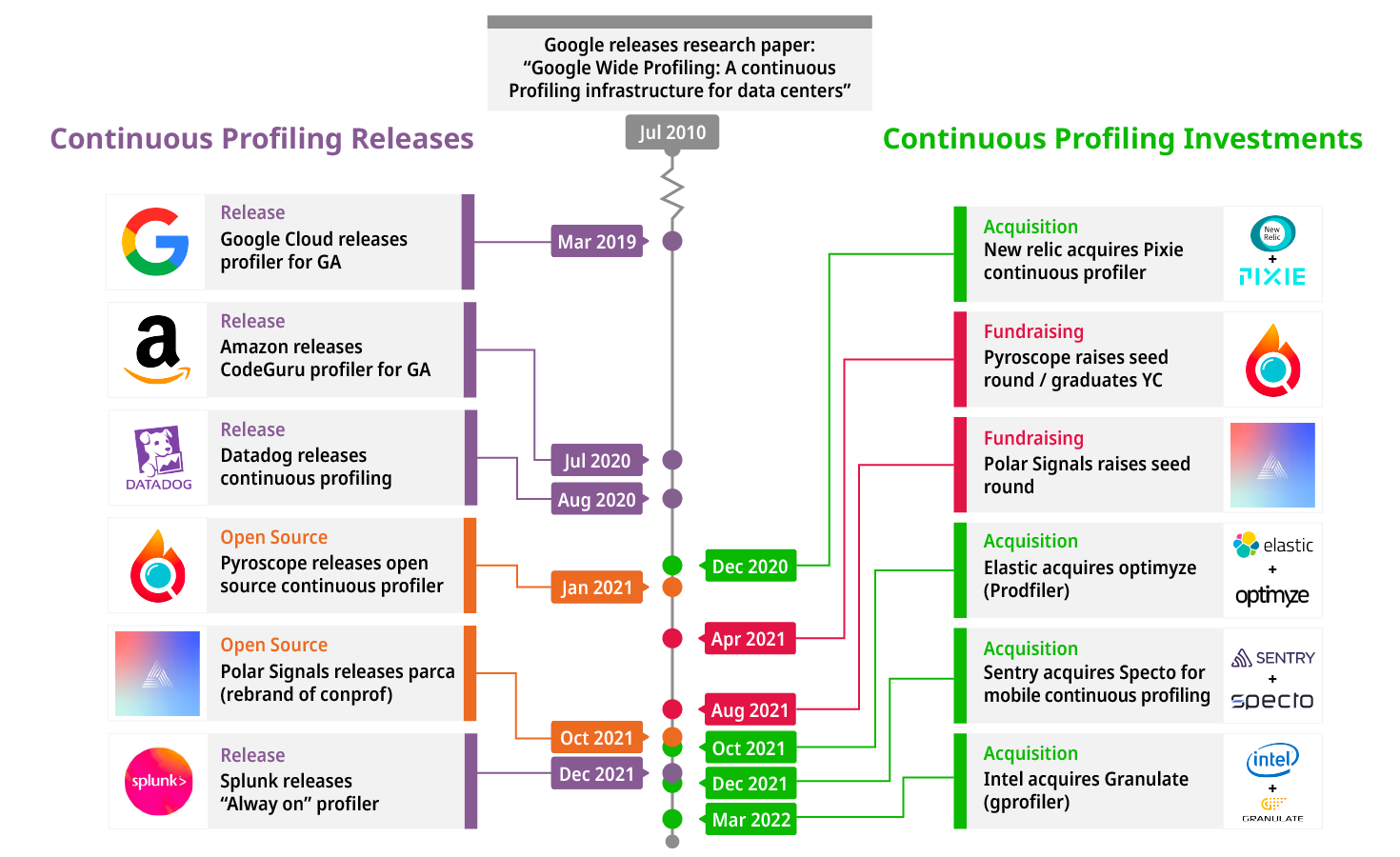
Grafana is an open-source observability and monitoring platform used by individuals and organizations to monitor their applications and infrastructures. Grafana leverages the three pillars of observability, metrics, logs, and traces, to deliver insights into how well your systems are doing. Nowadays, Observability involves a whole lot more than metrics, logs, and tracing; it also involves profiling.
In this article, I will:
- Describe how to leverage continuous profiling in Grafana by installing the Pyroscope flamegraph panel and datasource plugin
- Show how to configure the plugins properly
- Explain how to setup your first dashboard that includes profiling
- Give a sneak peak of an upcoming feature that will let you link profiles to logs, metrics, and traces
If you're new to flamegraphs and would like to learn more about what they are and how to use them, see this blog post.
Introduction#

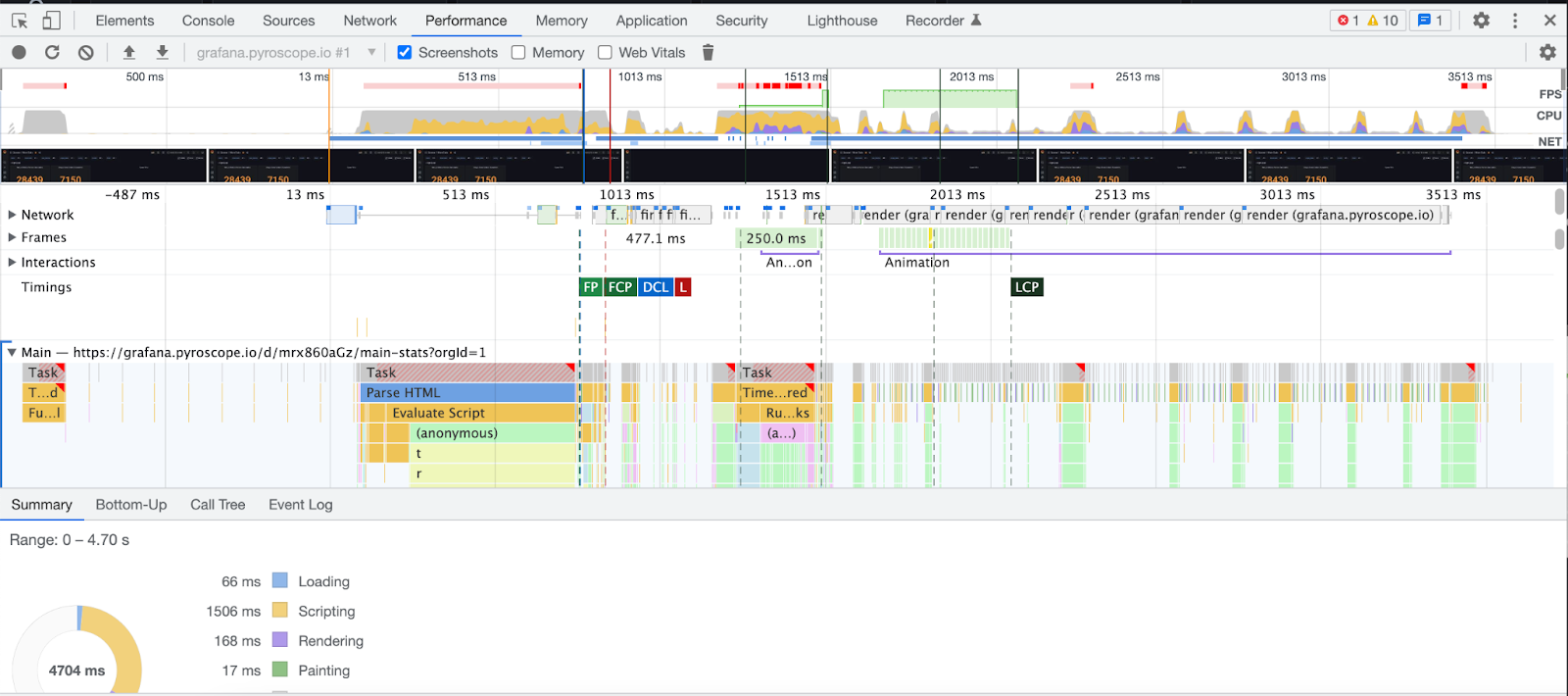
Grafana provides you with tools to visualize your metrics, view logs, and analyze traces, but it is incomplete without the added benefits of profiling. Continuous Profiling is super critical when you’re looking to debug an existing performance issue in your application. It enables you to monitor your application’s performance over time and provides insights into parts of your application that are consuming resources the most. Continuous profiling is used to locate and fix memory leaks, clean up unused code, and understand the call tree of your application. This results in a more efficient application.
Benefits of using Pyroscope in Grafana#
Unified view for complete observability#
Using Pyroscope in Grafana provides you with complete observability without leaving your Grafana dashboard. Grafana leverages the powerful features of Pyroscope to take complete control of your application’s end-to-end observability and makes things like debugging easy. You can now see your profiles alongside corresponding logs, metrics, and traces to tell the complete story of your application.
Zero migration cost#
It costs nothing to migrate your application profile from Pyroscope’s UI dashboard into Grafana. Simply open Grafana and install both the Pyroscope panel and datasource plugin, and you’re all set!